Energy and Grid Infrastructure
Verifiable trust for energy devices you manufacture, deploy, and operate at scale.

Energy systems increasingly depend on distributed devices making autonomous decisions: shedding loads, dispatching storage, reporting consumption, proving generation. The accuracy of these decisions depends entirely on trusting the data and the devices producing it.
Standard implementations store cryptographic keys in processor flash memory. An attacker with physical access can extract them. Firmware without integrity checks can be modified to inflate readings or fake generation data. A cloned device identity lets someone collect payments for energy never produced.
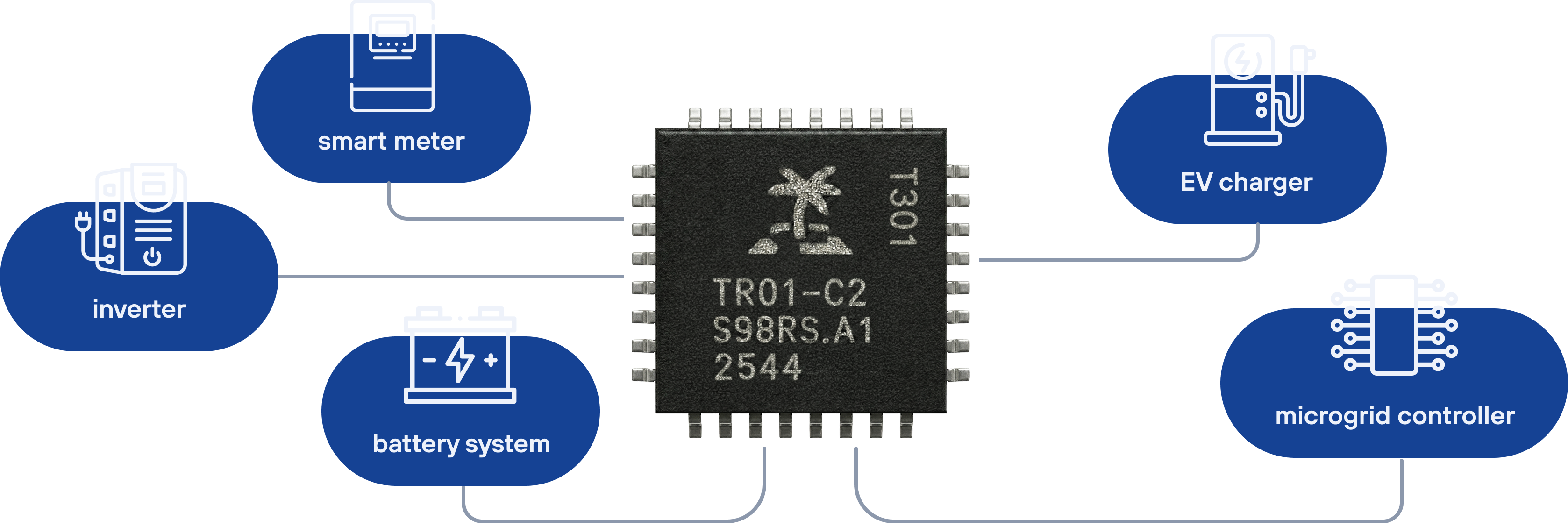
These risks play out across real infrastructure. Smart meters in utility cabinets, inverters on rooftops, battery controllers in basements, EV chargers in parking lots. Every device is physically accessible. Software-only protections fail because the operating system is the attack surface.
%20(1).jpg)
How TROPIC01 Enforces Energy and Grid Infrastructure
TROPIC01 for Energy Hardware
Signed Measurements at the Source
Energy readings drive financial settlements, grid balancing, and regulatory reporting. TROPIC01 signs measurement data inside the secure element. Each signature binds the reading to a verified device identity and firmware state. The signed data is tamper-evident from sensor to settlement platform.
Secure Key Storage for Autonomous Operations
Energy devices authenticate to networks, sign data, and exchange credentials with peer devices without human involvement. TROPIC01 stores operational keys in hardware. The chip supports hierarchical key derivation for TLS client certificates, IEC 62351 authentication, network encryption, and any protocol requiring persistent device credentials.
Secure Boot and Anti-Rollback
Immutable anchors in OTP memory verify firmware at every boot. Monotonic counters prevent version rollback. For fleets of thousands of devices, this eliminates downgrade attacks entirely.
Target Applications
Immutable anchors in OTP memory verify firmware at every boot. Monotonic counters prevent version rollback. For fleets of thousands of devices, this eliminates downgrade attacks entirely.