RDDL Network
Verifiable energy data from device to settlement.

"The real value is that it’s open, peer-reviewed, easy to use, and we didn't have to sign any NDAs for it. It was a really smooth integration, and that's what makes it outstanding on the market right now."
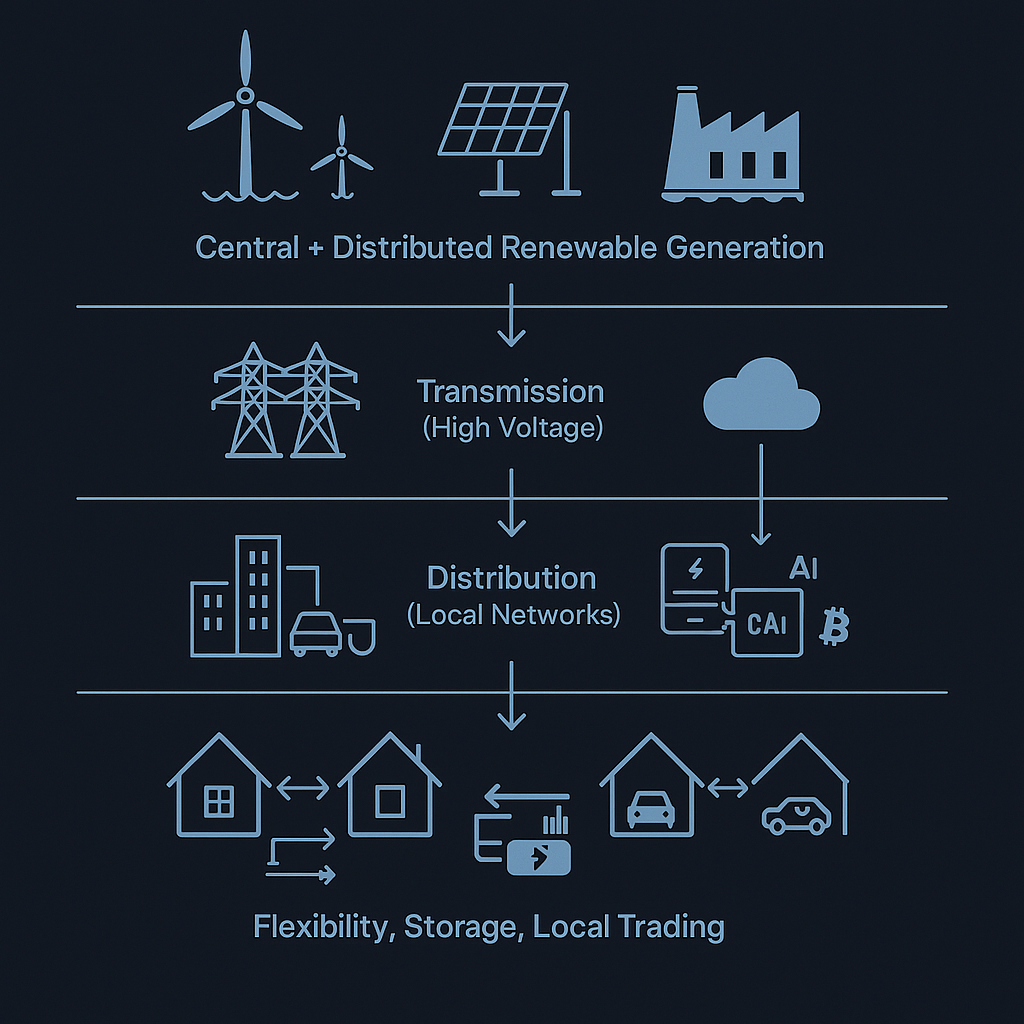
RDDL Network builds infrastructure that connects physical energy assets to digital settlement systems. Their devices measure energy production and consumption at sub-10-second intervals, sign the data cryptographically, and deliver it to systems that handle billing, grid balancing, and compliance reporting.
Distributed energy devices face a specific challenge. Smart meters sit in utility cabinets. Inverters mount on rooftops. Battery controllers live in basements. Every device is physically accessible. Every device must remain trustworthy without supervision. And when devices report to automated settlement systems, a compromised node can go undetected for months.
TROPIC01 in RDDL Hardware
Both devices use TROPIC01 as the hardware root of trust for identity, key management, and data signing.
Trusted Measurements at Scale
Device Identity That Cannot Be Cloned
Each device identity is physically bound to the chip through PUF-derived keys. Remote systems verify device authenticity through challenge-response protocols before trusting any measurement data. A key ceremony creates cryptographic identities and attests the association between public keys and the physical machine. No device can impersonate another.
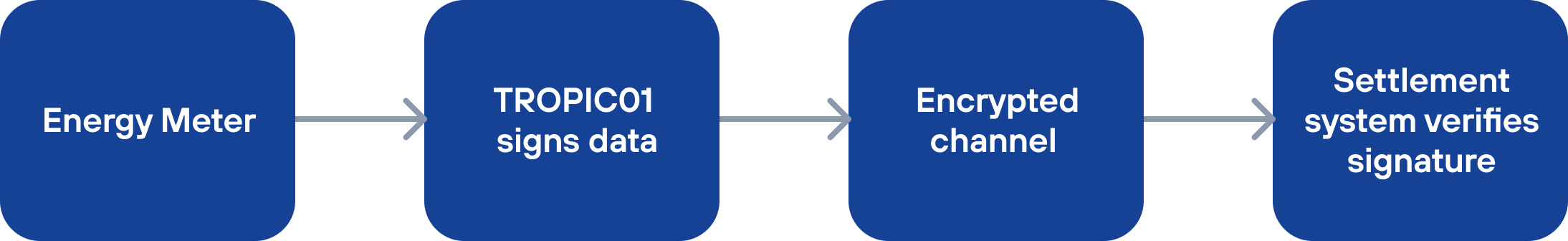
Cryptographically Signed Energy Measurements
TROPIC01 signs measurement data inside the secure element. Each signature binds the reading to a verified device identity and firmware state. Grid operators, aggregators, and settlement systems can verify data authenticity without trusting the network path. This provides proof that a specific device produced a specific measurement at a specific time.
Autonomous Key Management
RDDL devices sign data and authenticate to networks without human intervention. TROPIC01 stores all operational keys in hardware where they cannot be extracted. The chip supports hierarchical key derivation, creating separate key pairs for different networks from a single root seed. Private keys never leave the silicon.
Physical Attack Protection and Secure Updates
Hardware tamper detection protects devices in utility cabinets and shared equipment rooms. Monotonic counters enforce firmware version control, preventing rollback to vulnerable code across distributed fleets.